Important things to know
Most people don't plan to end up in cybersecurity.
It usually starts with curiosity. One video about a data breach turns into another about ransomware, and before you know it you're three hours deep into a rabbit hole about how attackers break into companies and how defenders stop them.
At some point the question hits: could I actually do this for a living?
For a lot of people, the SOC Analyst role is the first real doorway into the industry. The demand is genuine, a traditional computer science degree isn't always required, and the experience you build opens up multiple directions in security later on.
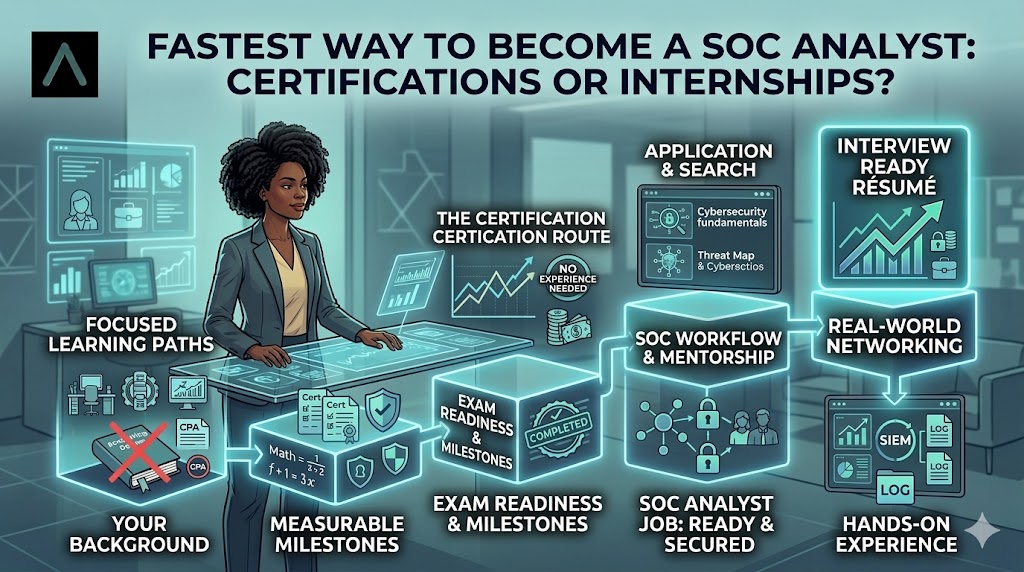
But once people decide they want to aim for a SOC role, they hit the same confusing question. Should you go after certifications first, or try to land an internship?
Strong opinions exist on both sides. Some say certs are everything. Others insist experience is the only thing that actually matters.
The honest answer sits somewhere in the middle.
What a SOC Analyst Actually Does
A Security Operations Centre is the security monitoring hub of an organisation. The team watches systems, networks, and applications around the clock for signs of suspicious activity.
As a Tier 1 analyst, which is where most people start, your job is to monitor alerts and figure out whether something unusual is genuinely a threat or just noise.
On a given shift you might be reviewing suspicious login attempts, investigating unusual network traffic, looking into a potential phishing incident, and escalating anything confirmed to a senior analyst or the incident response team. Most organisations run SIEM platforms like Microsoft Sentinel, Splunk, or IBM QRadar to collect logs and surface suspicious activity.
Some shifts are fast and chaotic when multiple alerts fire at once. Others are quieter, more methodical. You're reviewing logs and looking for patterns that might signal something worth investigating further.
When a real incident does happen, the SOC is usually the first team to see it.
What Certifications Actually Do For You
Certifications are often the first thing people reach for when they decide to move into cybersecurity, and they do serve a real purpose. They show employers you've taken the time to learn the fundamentals. They get you through the CV filter when a recruiter is scanning a pile of applications and looking for something recognisable.
For SOC roles in the UK, the certifications that come up most often are CompTIA Security+, Microsoft SC-200, and CompTIA CySA+. Security+ is probably the most common starting point. It covers network security, threat identification, identity management, and incident response basics. The SC-200 is worth paying attention to if you want to work with Microsoft Sentinel specifically, which a significant number of UK organisations use. For complete beginners, the ISC2 Certified in Cybersecurity qualification has become a popular first step before moving on to anything more advanced.
Here's the thing though. Certifications help you get noticed. They don't automatically make you job-ready.
You can pass Security+ and still feel completely lost the first time you're sitting in front of real SIEM alerts trying to figure out what you're actually looking at. That gap between passing an exam and doing the work is something a lot of people experience, and it's worth being honest about it before you spend several hundred pounds on an exam voucher.
Why Internships Fill the Gap
This is where internships become genuinely valuable. They put you inside a real security team where you can see how analysts actually work, not just read about how they're supposed to work.
Instead of studying incident response in theory, you're watching how alerts get triaged, how investigations get documented, and how the team responds when something suspicious is actually confirmed. That context is hard to replicate anywhere else.
It also gives you something concrete to talk about in interviews. There's a significant difference between telling a hiring manager you hold a Security+ certification and telling them you helped investigate a phishing campaign that affected multiple employee accounts and assisted with documenting the incident response. Both are worth saying. But one of them is a story.
In the UK, early-career cybersecurity placements come from a few different places. The NCSC's CyberFirst initiative is one of the more underused options, particularly for students. Government and public sector organisations like GCHQ and NHS Digital run their own schemes too. And don't overlook smaller MSSPs. At a large enterprise you might spend a whole placement on one narrow task. At a smaller managed security provider you'll likely get exposure to a much wider range of clients and incident types.
If You Can't Get an Internship Right Now
Not everyone can access a placement immediately, and that's exactly the problem Amdari's work experience programme was built to solve.
Rather than spending months on simulated labs hoping something sticks, Amdari puts you inside real security workflows with structured mentorship and hands-on tasks that mirror what Tier 1 analysts actually do on the job. You're not just practising in isolation. You're building documented experience you can genuinely talk about in interviews. Watch testimonials here. For anyone who keeps getting told they need experience to get experience, this is the way around that wall. Book a free clarity call with our team to know how to get started.
So Which One Should You Go For First?
If you're completely new to IT, starting with a certification makes sense. Something like Security+ or ISC2 Certified in Cybersecurity helps you understand the basic language and concepts before anything else. Without that foundation, even hands-on practice can feel confusing.
If you already work in IT, whether that's helpdesk, networking, or sysadmin work, you may have more transferable knowledge than you realise. Adding a security-focused certification and starting to apply for SOC roles or internships could be a natural next step without needing to start from scratch.
Students often do well pursuing both at the same time, studying for a certification while actively running an internship and early career programmes.
There's no single perfect path. But the people who tend to break through are the ones who combine structured learning with hands-on practice as early as possible, rather than waiting until they feel completely ready.
What the Money Looks Like
Entry-level SOC Analyst roles in the UK generally start between £22,000 and £32,000, depending on the organisation and location. After a few years of solid experience, mid-level analysts often move into the £35,000 to £50,000 range, particularly those who develop strong skills in threat detection or incident response. Senior analysts and detection engineers can earn significantly more.
One of the real advantages of starting in a SOC is the number of directions you can move into afterwards. Incident response, threat intelligence, cloud security, penetration testing - the skills you build in security operations carry across a lot of different specialisms.
A lot of people who eventually land their first cybersecurity role don't have a perfect background. They didn't always tick every box on the job description. What they had was enough foundational knowledge, some evidence they could do the work, and the persistence to keep going when the path wasn't obvious.
The UK cybersecurity skills gap is very real. Organisations are actively looking for people willing to put in the effort to learn.
Amdari's SOC Analysis work experience programme is built around getting people job-ready, not just exam-ready. If you're serious about starting a career in security, take a look at what we offer. Your SOC experience isn't just a job title. It's a launchpad. Book a free tech consultation call with our team to know the structure of this program and why you need it especially if you are an African immigrant, struggling to land SOC roles due to a lack of UK, US or Canada work experience. Click here to get started.