Important things to know
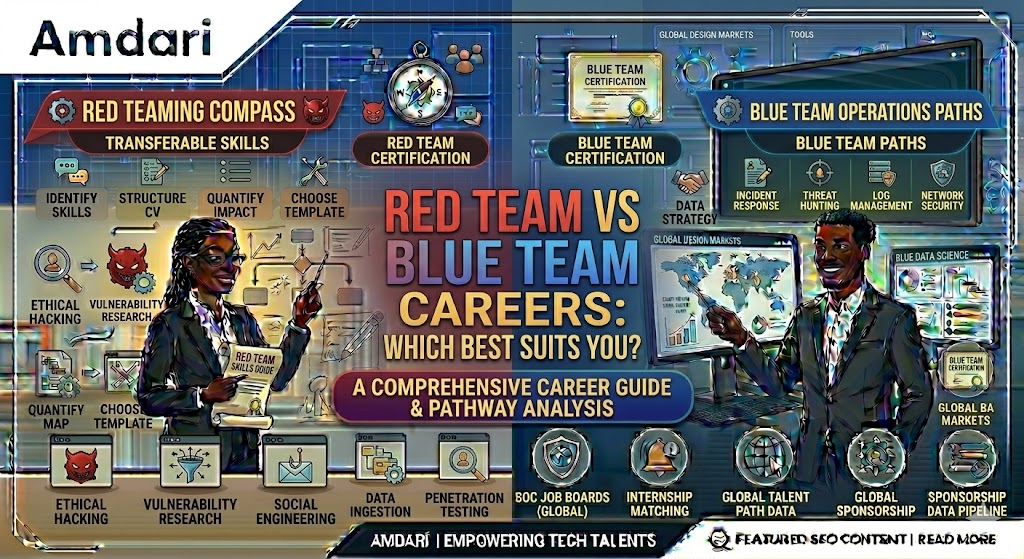
It’s no news that generic advice flies around a lot in cybersecurity. Red team this; blue team that.
Follow this roadmap, get these certifications. I won’t add to the noise. I’ve spent years mentoring people trying to figure out where they fit, and I’ve seen where most of them get it wrong. So let’s keep this simple and real.
The first mistake people make is that they try to choose a path too early without touching real environments.
They haven’t struggled through a broken lab, they haven’t seen how attacks actually play out but they already want to “specialize” and that is the mistake.
What the Industry Actually Cares About
Nobody serious is asking what side you picked. They care about things like:
- Can you find problems?
- Can you understand what’s happening?
- Can you respond when something breaks?
- Can you explain it clearly to someone non-technical?
That’s the job. Not labels.
Red Team: What It Really Feels Like
Red Team is not just “hacking”. It’s a lot of trying something, watching it fail, adjusting, trying again over and over. You’re thinking through systems, not just attacking them and when you finally get in, that’s not the end.
You still have to explain: What you did, why it worked and what it means for the business. Most people don’t prepare for that part.
Blue Team: What People Underestimate
Blue Team is where you actually see how messy things get.
Logs everywhere, alerts firing, half of them, useless. You have to decide: Is this real? is this noise? Do we act now or monitor? That pressure is real and if you stay in it long enough, you start to understand attackers properly, not from theory but from patterns.
What Actually Made Me Better
One philosophy changed how I approached both sides:
Go deeper in a niche before going wider. Most people try to learn everything at once. Web, network, cloud, AD, Malware. They touch everything and master nothing.
What actually works is when you pick one area, stay there longer than you’re comfortable, break it, and understand it properly. That depth does something important, it sharpens how you think and once that thinking is solid, moving into other areas becomes easier. That’s what made me better across both Red and Blue; not trying to do everything early.
Where Most People Get It Wrong
They chase roles instead of building capability.
“I want to be a Red Teamer.”
“I want to be a Blue Teamer.”
But when you look closely, you’ll clearly see; weak fundamentals, no real lab experience, no depth in anything. So even when opportunities come, they struggle to perform.
Don’t rush to label yourself, instead, build depth somewhere first, then expand. If you like attacking, go deeper into one area; i.e, web, AD, whatever it is. If you like defense, go deeper into logs, detection, incident response but stay long enough to actually understand what you’re doing. That’s where the real growth happens.
This is something we push heavily at Amdari. We don't just focus on exposure but also depth, real environments, real problems, real expectations because if you don’t go deep at least once, everything else stays surface level and surface-level knowledge doesn’t hold in real work.
Red Team vs Blue Team is not the real question. The real question is: Have you gone deep enough to actually understand anything yet? Because once you do, the path becomes clearer, your confidence improves and your skill starts to show. Until then, don’t rush it. Build depth first then expand. You can start by booking a free charity call with our team of consultants to help you build depths. Click here to book a call.