Important things to know
If you have spent any time in cybersecurity communities, online or otherwise, you have probably noticed that these two roles get conflated constantly. People use them interchangeably, assume one leads naturally into the other, or pick one without really understanding what the day-to-day actually looks like. That confusion is worth clearing up, because the skills overlap in places but the mindset, the work, and honestly the personality fit are quite different.
This is not a post about which one is better. It is about helping you understand what you are actually signing up for before you commit months of study time to a path that might not suit how you think.
The fundamental difference is direction
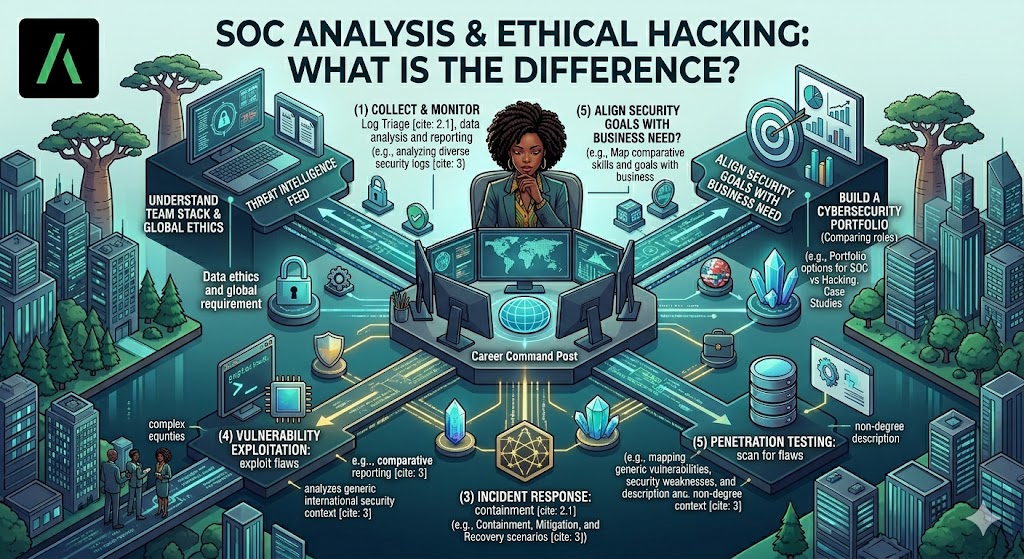
The simplest way to frame it is this: a SOC analyst is watching the door. An ethical hacker is trying to break through it. SOC analysts work in detection and response. Their job is to monitor environments, identify when something has gone wrong or is going wrong right now, and respond to it. Ethical hackers, more formally called penetration testers, are hired to simulate what an attacker would do before a real attacker gets the chance. One role is reactive and continuous. The other is project-based and offensive.
That distinction sounds simple on paper, but it shapes everything from the tools you use to the hours you work to the way you approach a problem.
What a SOC analyst actually does
A SOC analyst is essentially a constant presence. Alerts come in, and your job is to triage them, investigate the ones that matter, escalate where necessary, and document everything. On a quiet day, you are tuning detection rules, reviewing dashboards, and making sure your visibility is where it needs to be. On a bad day, you are in the middle of a live incident, correlating logs across multiple data sources, trying to establish a timeline before the damage gets worse.
The work requires patience more than anything else. You will see a lot of false positives. You will spend time understanding what normal looks like in an environment so that you can recognise when something is not. The analytical muscle you build is about pattern recognition, log interpretation, and being able to communicate clearly under pressure because incidents do not happen in isolation and you will always be working with other people.
SIEM platforms, endpoint detection tools, threat intelligence feeds, and case management systems are your daily environment. Knowing how to move across all of them quickly and confidently is what separates an effective analyst from someone who is just processing tickets.
What an ethical hacker actually does
A penetration tester approaches an environment with a fundamentally different question: where can I get in, and how far can I go once I am there? The work is structured around engagements, scoped assessments where a client defines what can be tested and a tester works methodically through it, documenting vulnerabilities, demonstrating impact, and writing a report that a business can actually act on.
In practice that means reconnaissance, scanning, exploitation, and post-exploitation work. You are thinking about attack chains, about how one misconfiguration or weak credential leads to the next foothold. You need to understand how systems work well enough to understand how they fail.
The soft skill that people underestimate in this role is the report. An ethical hacker who cannot write clearly is significantly less valuable than one who can, because the entire point of the exercise is that someone on the client side needs to understand what was found, why it matters, and what to do about it. Technical findings that cannot be communicated to a non-technical stakeholder do not get fixed.
Where they overlap
Both roles require a solid foundation in how networks work, how attackers operate, and how to think systematically about security. A SOC analyst who understands how attacks are constructed is better at spotting them. An ethical hacker who understands how defenders think and monitor is better at simulating realistic adversaries and not just running automated scans against a target.
Frameworks like MITRE ATT&CK sit at the centre of both disciplines. Threat intelligence matters in penetration testing just as much as it does in a SOC context. And the fundamentals: TCP/IP, Active Directory, web application behaviour, common vulnerability classes, are common ground.
The difference is not really in the knowledge base. It is in how you apply it and what kind of work environment suits you.
How to figure out which one is for you
If you like the idea of being the person who finds the problem before anyone else does, working in short intensive bursts on defined targets, and spending a lot of time reading documentation to understand how something is supposed to work so you can figure out how it does not, penetration testing is probably the right direction.
If you are more drawn to continuous monitoring, pattern recognition over time, being at the centre of an incident response and piecing together what happened from fragments of evidence, the SOC analyst path tends to suit people who think that way.
Neither is an entry-level role in the sense that you walk in knowing nothing. Both reward people who have done genuine hands-on work and can demonstrate it.
At Amdari, we run both tracks for exactly this reason. The Ethical Hacking and Penetration Testing programme and the SOC and Threat Intelligence programme are structured separately because the skills and the mindset they develop are genuinely different. Interns work on real scenarios relevant to each discipline, get mentorship from practitioners, and come out with experience they can talk about in interviews with specificity rather than generality. Watch testimonials here. If you are still figuring out which direction suits you, spending time inside both programmes is one of the better ways to find out. Most people know pretty quickly once they are doing the actual work but you can book a free clarity call with our team here.